Today, biometric authentication is redefining the way we safeguard our sensitive information. As traditional password-based systems reveal vulnerabilities, biometric authentication steps into the spotlight, offering a more secure and user-friendly approach to identity verification. This article explores the intricacies of biometric authentication, its diverse applications, the underlying technologies, and the potential it holds in revolutionizing the landscape of digital security.
Understanding Biometric Authentication
Biometric verification leverages unique biological or behavioral traits to confirm an individual’s identity. Unlike traditional methods reliant on passwords or PINs, biometric systems employ characteristics such as fingerprints, facial features, iris patterns, voiceprints, and even behavioral traits like typing patterns or gait recognition. The fundamental idea is that these biological markers are inherently unique to each individual, providing a robust and personalized means of authentication.
1. Fingerprint Recognition

Fingerprint recognition is one of the most widely adopted forms of biometric authentication. The distinct ridges and valleys on an individual’s fingertip create a unique pattern that can be captured and stored for identification purposes. Fingerprint scanners, commonly found on smartphones and access control systems, compare the presented fingerprint with the stored data to grant or deny access.
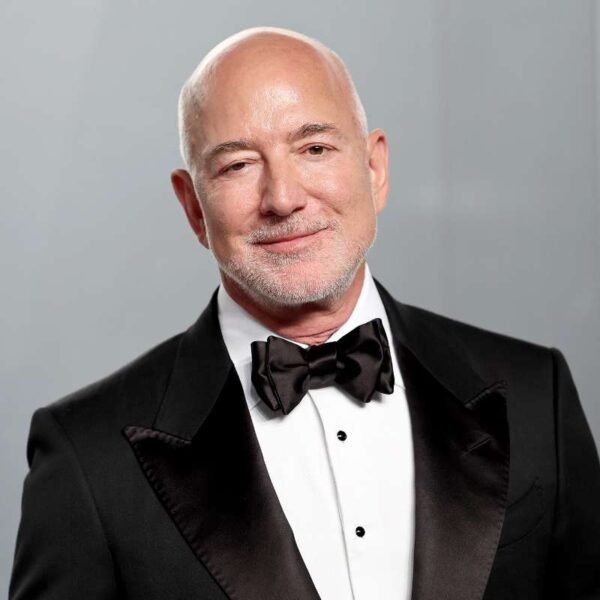
2. Facial Recognition
Facial recognition technology analyzes the unique features of an individual’s face, such as the arrangement of eyes, nose, and mouth. Advanced algorithms translate these features into a unique facial template, which can then be used for identification. Facial recognition has found applications in smartphone unlocking, airport security, and even social media tagging.
3. Iris Recognition
Iris recognition relies on the intricate patterns within the iris of an individual’s eye. The unique characteristics, such as the arrangement of furrows and crypts, are captured using specialized cameras and converted into a template for identification. This method is highly accurate and is often employed in high-security environments.
4. Voice Recognition
Voice recognition technology analyzes the unique vocal patterns, pitch, and tone of an individual’s voice. This biometric modality is often used for telephone-based authentication and voice-controlled devices. Voice recognition systems can identify individuals based on specific vocal characteristics, making it a valuable tool for secure communication.
5. Behavioral Biometrics
Behavioral biometrics focus on unique patterns in an individual’s behavior, such as typing rhythm, mouse movement, or even gait recognition. These traits provide an additional layer of security as they are harder to replicate or forge. Behavioral biometrics are often employed in continuous authentication systems that continuously monitor user behavior during a session.
What are its Applications?
The applications extend across various industries, providing enhanced security and user convenience.
1. Mobile Devices

Smartphones have become a ubiquitous part of our lives, and biometric authentication has become a standard feature for unlocking devices and securing sensitive data. Fingerprint scanners, facial recognition, and iris recognition are now integrated into many modern smartphones, offering users a quick and secure way to access their devices.
2. Financial Services
The financial sector has embraced biometric authentication to enhance the security of transactions and account access. Biometric identifiers add an extra layer of protection for online banking, mobile payment apps, and ATM transactions. This not only reduces the risk of unauthorized access but also simplifies the user experience.
3. Government Identification
Biometric authentication has become integral to government identification systems, such as passports and national ID cards. The use of fingerprints, facial recognition, and iris scans in these documents enhances the accuracy of identity verification, making it more difficult for individuals to falsify or duplicate official credentials.
4. Healthcare
In the healthcare sector, biometric authentication ensures secure access to patient records and sensitive medical information. Hospitals and healthcare facilities use biometric systems to authenticate healthcare professionals and restrict access to confidential patient data, safeguarding sensitive information from unauthorized individuals.
5. Access Control and Physical Security
Biometric authentication plays a crucial role in access control systems for secure facilities. Fingerprint scanners, iris recognition, and facial recognition are deployed to grant or deny access to restricted areas. This is particularly valuable in corporate environments, government facilities, and critical infrastructure where stringent security measures are essential.
How The Technology Works
The effectiveness of biometric authentication hinges on sophisticated technologies that capture, process, and compare biometric data.
1. Sensor Technology
Biometric sensors are at the forefront of capturing accurate and detailed biometric data. For fingerprint recognition, capacitive or optical sensors capture the unique ridge patterns. Facial recognition and iris recognition rely on high-resolution cameras to capture and process facial features or iris patterns. Voice recognition utilizes specialized microphones to capture the unique characteristics of an individual’s voice.
2. Pattern Matching Algorithms
Pattern-matching algorithms play a crucial role in comparing the captured biometric data with stored templates for identification. These algorithms analyze the intricate details of fingerprints, facial features, or iris patterns, determining the level of similarity between the presented biometric data and the stored reference data. Advancements in machine learning and artificial intelligence have significantly improved the accuracy and speed of these algorithms.
3. Template Storage and Encryption
Biometric templates, the digital representations of biometric features, must be securely stored to prevent unauthorized access. Encryption techniques are employed to protect these templates, ensuring that even if they are compromised, the original biometric data cannot be reconstructed. Secure storage is paramount to maintaining the integrity of biometric verification systems.
Challenges and Considerations
While biometrics offers a robust approach to identity verification, it is not without challenges and considerations.
1. Privacy Concerns
The collection and storage of biometric data raise privacy concerns, as individuals may be hesitant to share such sensitive information. Striking a balance between enhanced security measures and respecting privacy rights is essential for the widespread adoption of biometric verification.
2. Vulnerability to Spoofing
Biometric systems are not entirely immune to spoofing attempts, where individuals try to deceive the system using replicas or altered versions of biometric features. Continuous advancements in anti-spoofing technologies are crucial to mitigating this risk and ensuring the integrity of biometric verification.
3. Standardization
The lack of universal standards for biometric data formats and interoperability poses challenges, especially in cross-border applications. Standardization efforts are necessary to ensure seamless integration and compatibility of biometric systems on a global scale.
4. User Acceptance
The success of biometric authentication relies on user acceptance and confidence in the technology. Education and awareness initiatives are essential to dispel myths, address concerns, and build trust in biometric systems.
Future Trends and Innovations
As technology continues to advance, the future of biometric verification holds exciting possibilities.
1. Multimodal Biometrics
Combining multiple biometric modalities, known as multimodal biometrics, enhances security and accuracy. Integrating fingerprint recognition with facial or iris recognition, for example, creates a more robust authentication system, reducing the likelihood of false positives or negatives.
2. Continuous Authentication
Continuous authentication goes beyond a one-time verification and continuously monitors user behavior throughout a session. This dynamic approach adds an extra layer of security, ensuring that access is maintained only as long as the user’s behavior aligns with established patterns.
3. Wearable Biometrics
The integration of biometric verification into wearable devices is gaining traction. Smartwatches and fitness trackers equipped with biometric sensors provide a convenient and secure means of authentication, especially in scenarios where traditional methods may be impractical.
Conclusion
Biometric authentication represents a paradigm shift in the realm of identity verification, offering a secure, convenient, and personalized approach to safeguarding sensitive information. From fingerprints to facial features, the uniqueness of biological and behavioral traits forms the bedrock of this transformative technology.